Lets say you’ve become comfortable in your ability to recognize phishing email. You’re able to spot the strange “From” address hidden behind the reassuring “Billing Department” or “Customer Service” label that’s been applied. And even if that looks like it might be legit you know how to hover over links in the email and recognize something that says it came from Amazon should have amazon.com/ as the last part of the web address that comes before that very first single forward slash, “/”.
A business web address should always be https://businessname.com/maybemore or https://www.businessname.com/maybemore or https://businessname.org/maybemore and so on. The critical part of the address that tells you where the link will take you is between the paired // and the very first single /.
What do you do when everything looks legit? The “From:” doesn’t look strange, the subject isn’t alarming.
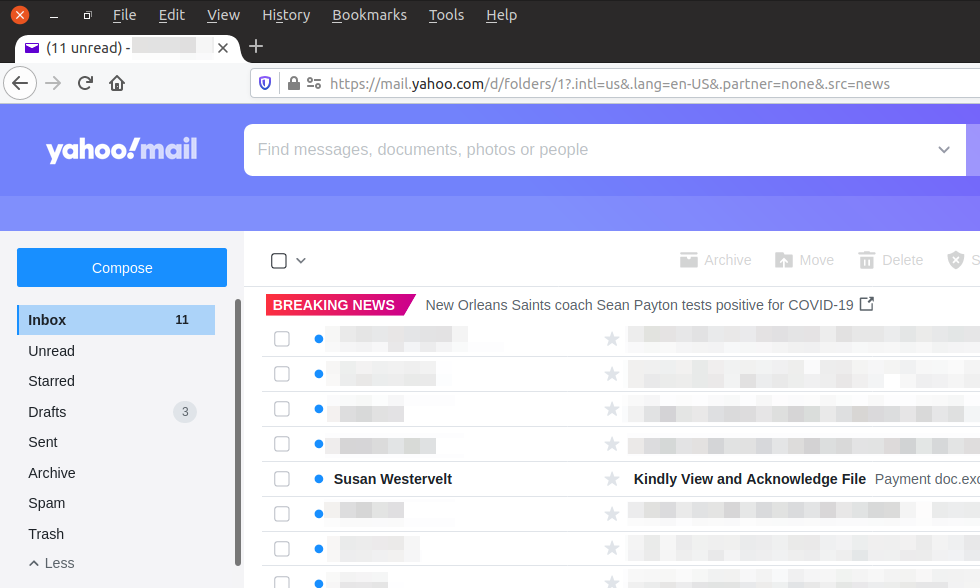
The message itself doesn’t try and make you panic. You can see the full email address and it looks legit. There’s no business website listed in the message but the part of the email address after the @ looks legit. And if you put the part after the @ into your web browser it does go to a legit website, in this case “equitybrands.com”.
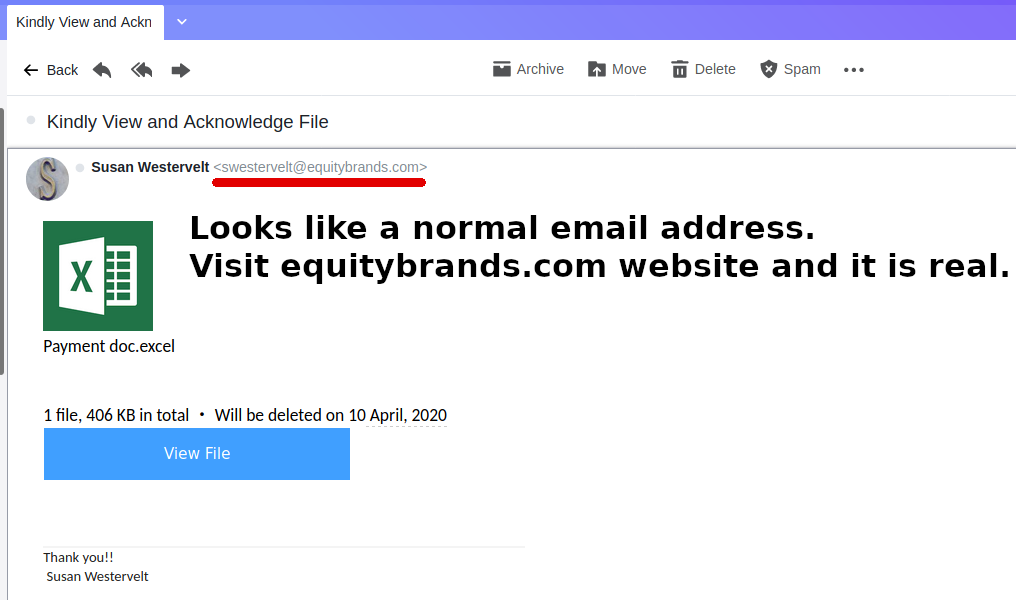
Stop right now! There’s no contact info provided in the message. No corporate website identified. No contact phone or email provided. And there’s no info what this is about. Did you buy something and there’s a payment issue, forget to return something, detail about a pending refund…? There’s just nothing except a big blue “View File” button.
In case you can’t resist taking a peek at the “Payment doc.excel” file I did it for you.
It isn’t a regular Excel file because the last part of the file name would be .xls or .xlsx. Sorry but you do need to know that. Ignoring all this I clicked the “View File” button. It got me to the screen below.
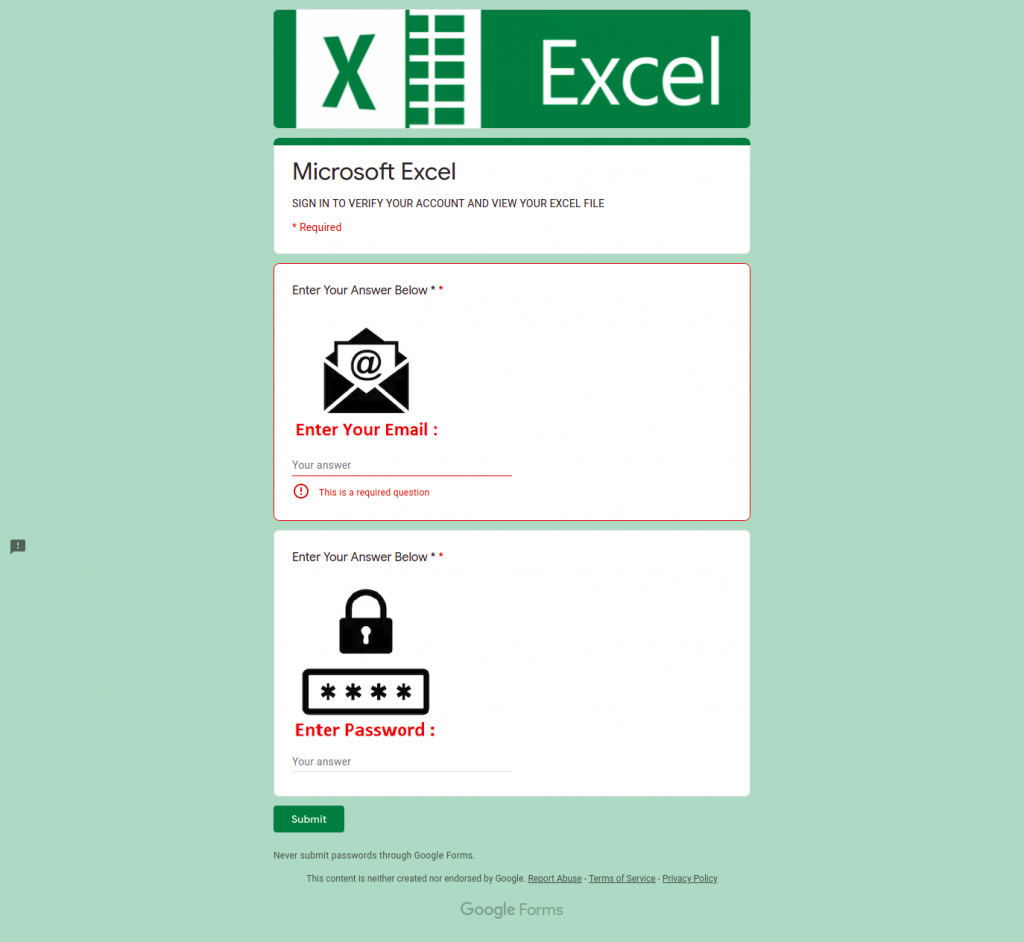
If you haven’t got suspicious yet you should turn and run now.
There’s no identifying information for the company.
Why are you being asked for your email? It came to your email. Why is it asking for that now?
What password do you need to enter? Since your email is asked for it seems like a reasonable password would be your email password. Don’t!! Your email password is to get into YOUR email. Nobody else needs that.
Then there’s a conflicting statement at the bottom of this web page. See just below the “Submit” button? It says “Never submit passwords through Google Forms.” That’s because this phishing message is bringing you to a Google Form to collect your email and password. The criminal can’t prevent Google from showing you that warning on a Google Form but they’re hoping you won’t see it or will ignore it.
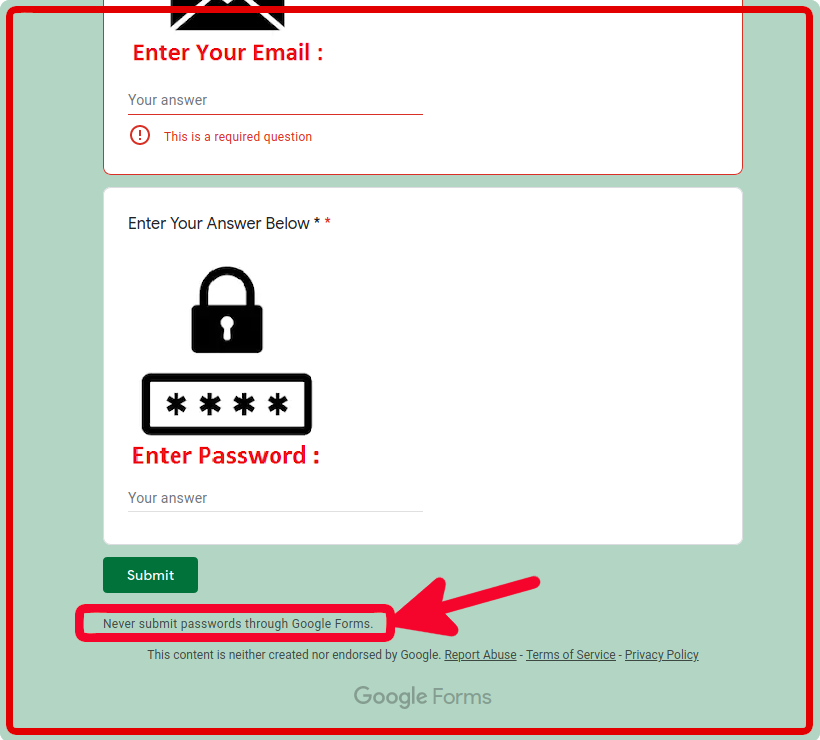
In summary, even if everything looks legit, if you’re asked to enter your email and password somewhere and you got there by clicking a link in an email DON’T DO IT!
Email and password are for you to get into your accounts. Don’t give them up at a website you got to by an email link.
Always go to the website your usual way and login. Then check your account to see if anything is needed.
If it isn’t a website you remember having an account at do not, do not, do not provide credentials to login. Call the business and ask what’s up!